Security Risk Analysis templates provide an effective and structured security evaluation framework. These templates outline key variables and steps required for a comprehensive risk assessment. Effective security risk analysis begins with identifying the types of threats your organization is most vulnerable to, assessing the overall impact that a potential threat may have, and finally evaluating the likelihood of an attack based on history and related data.
A security Risk Analysis template considers these factors by providing a clear process for categorizing, assigning weight to, and prioritizing risks. Ultimately, these templates help organizations optimize their resources to create greater resilience against potential cyberattacks while allowing them to focus more attention on strategic initiatives. In this article, you’ll find a collection of free Printable Security Risk Analysis Templates and samples in PDF, Word, and Excel format to help you make your security effective.
Download Free Security Risk Analysis Templates
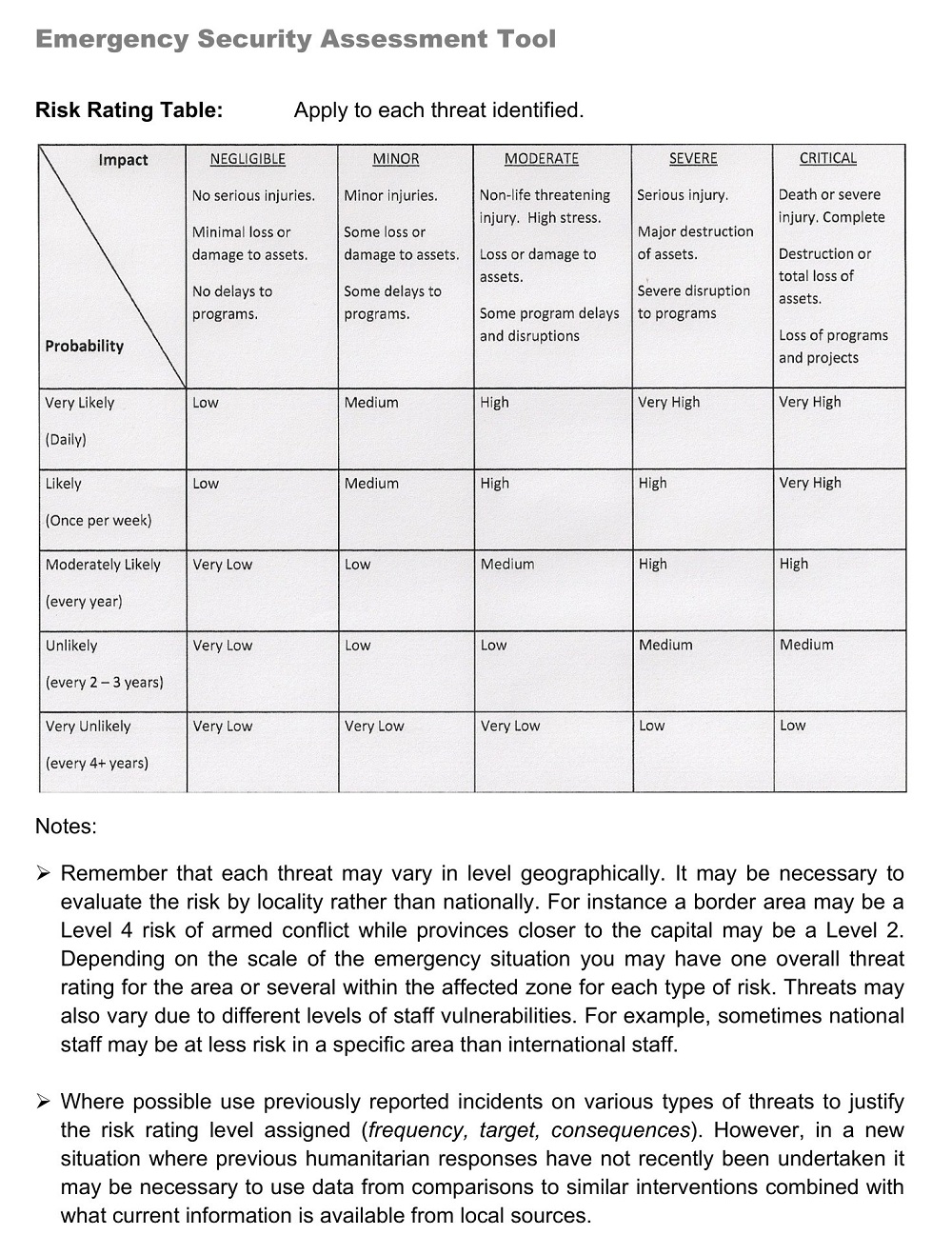
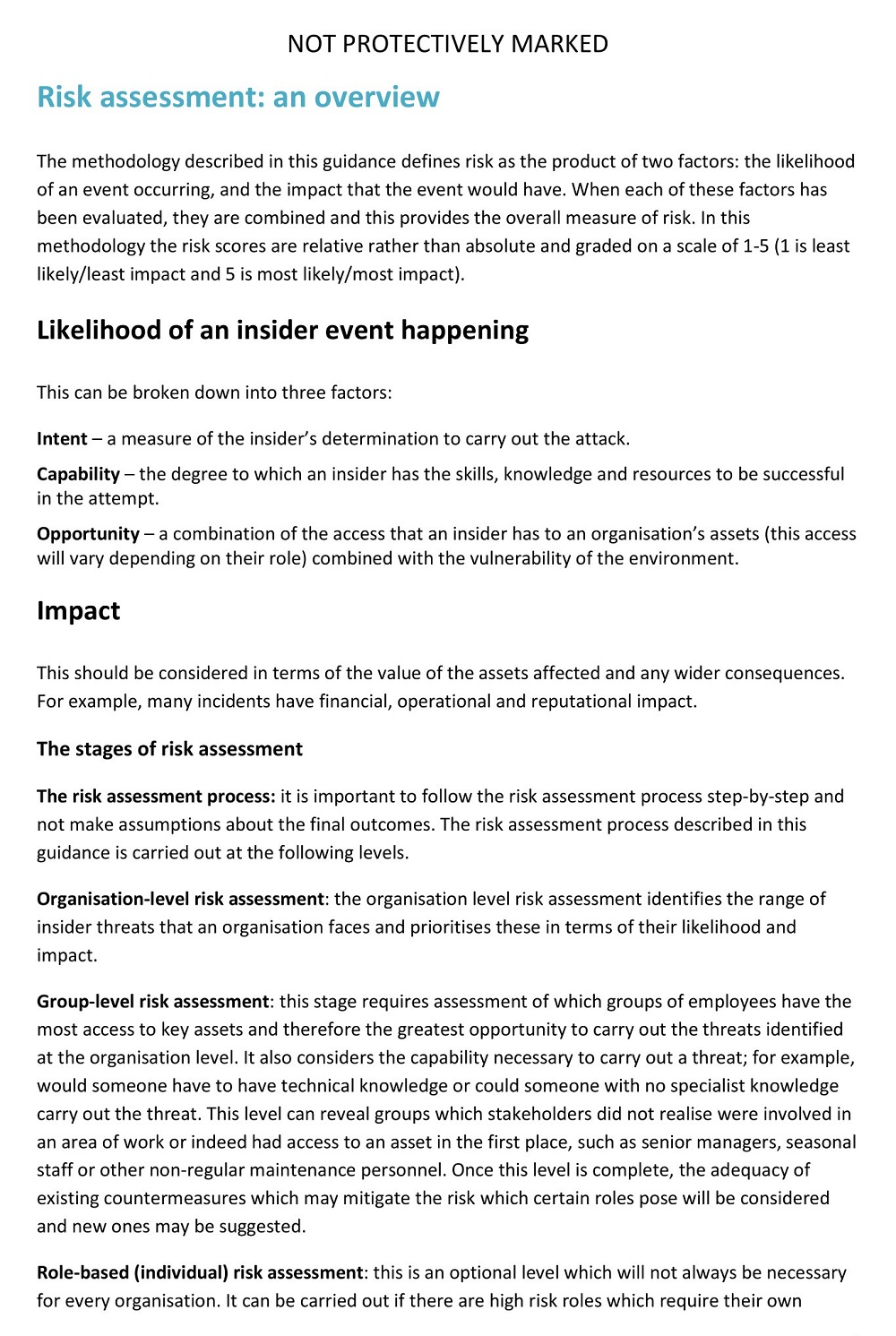
ACT Alliance Security Risk Assessment Tool
|
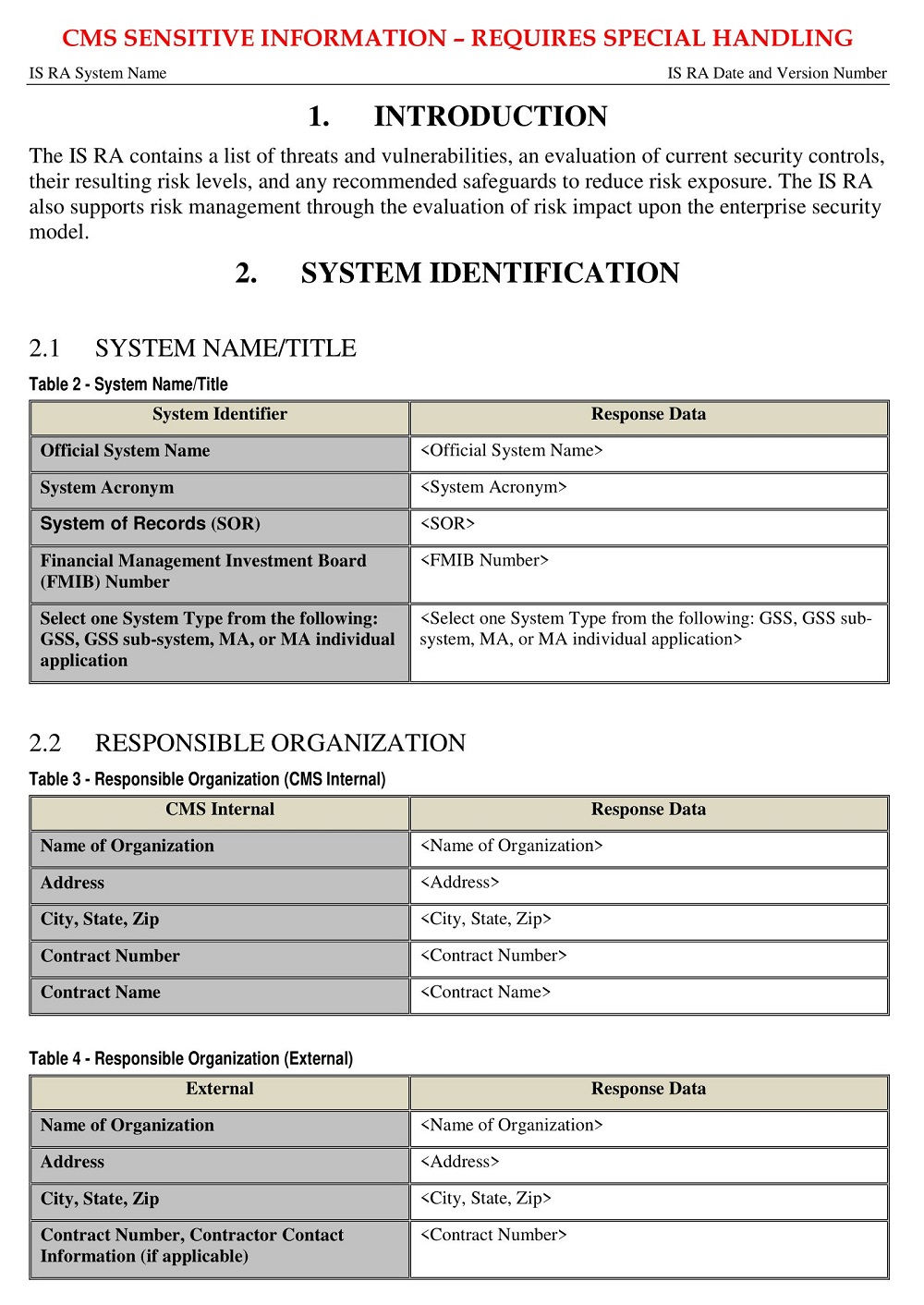
CMS Application Information Security Risk Assessment
|
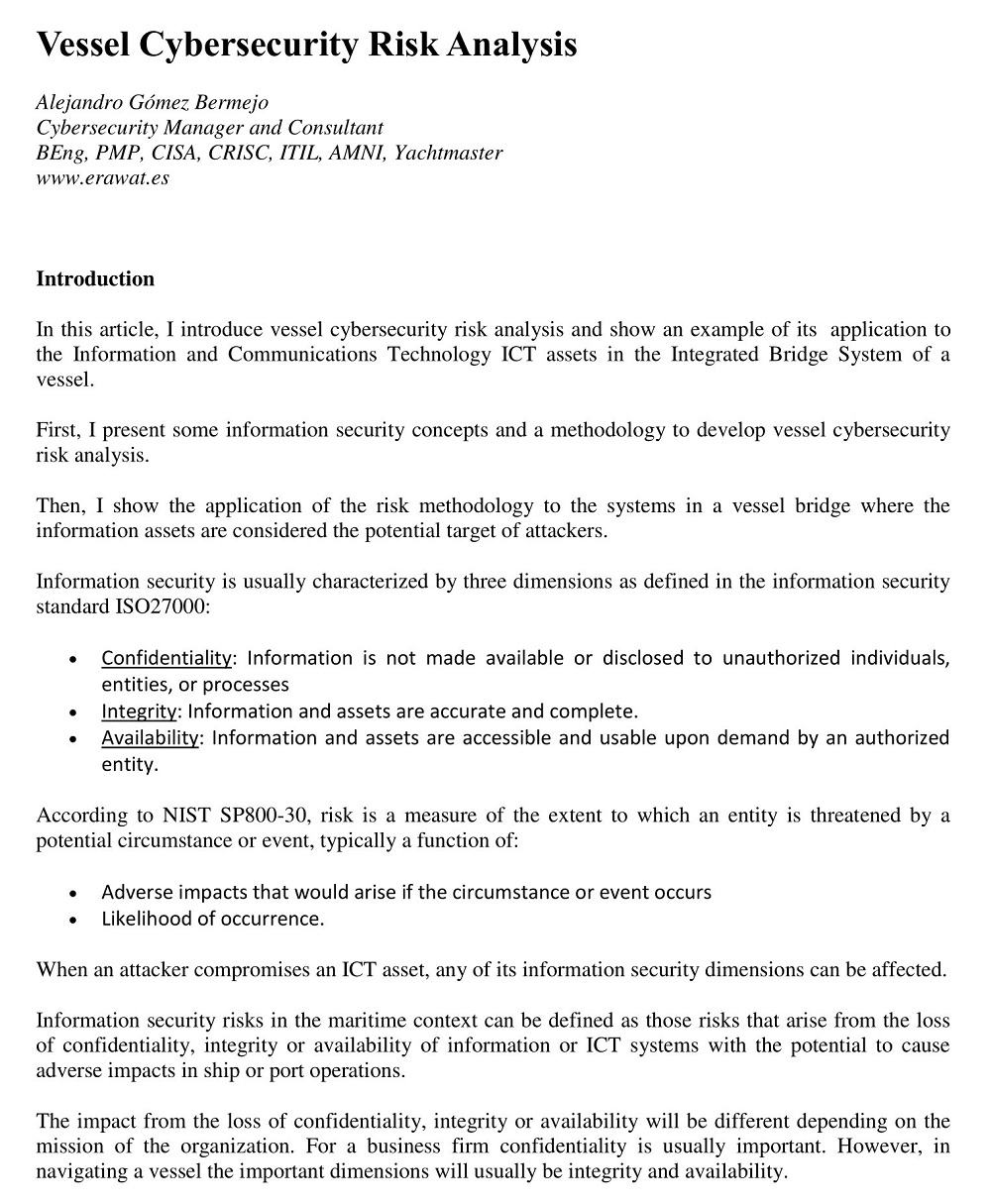
Cyber Security Risk Analysis Template
|
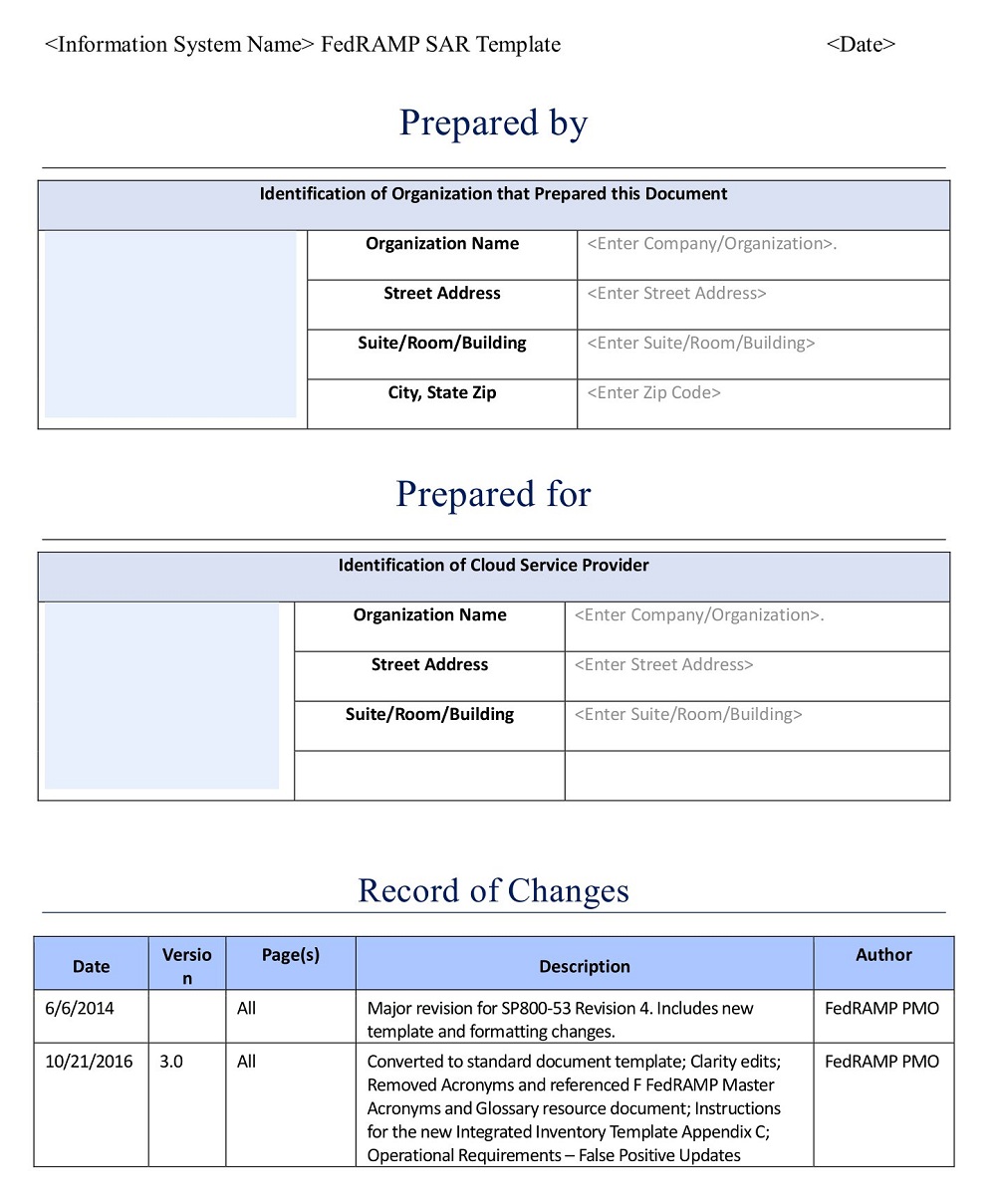
FedRAMP Seccurity Assement Report Template
|
Financial Security Risk Assessment Template
|
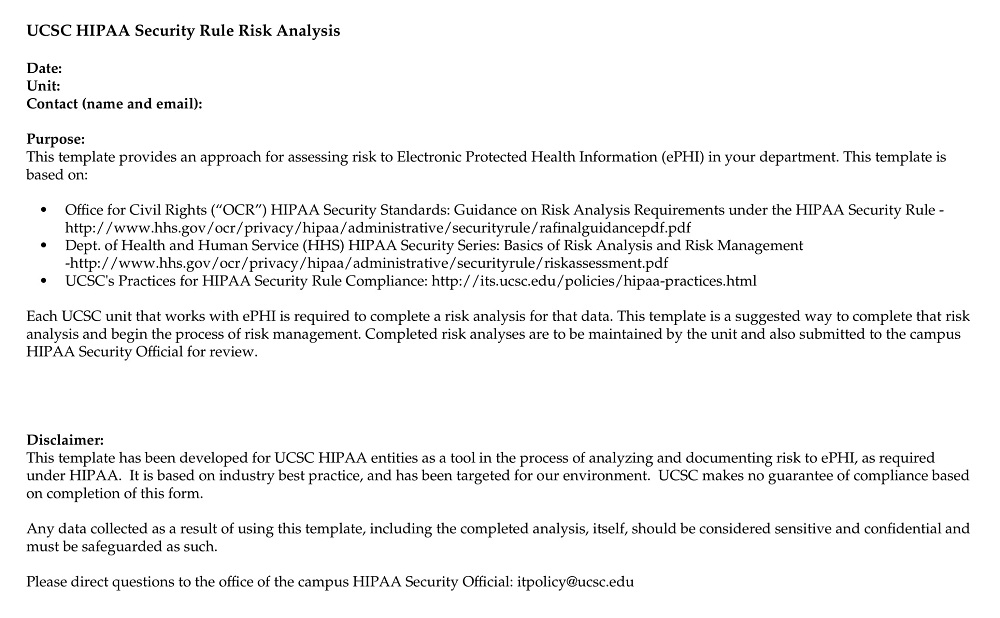
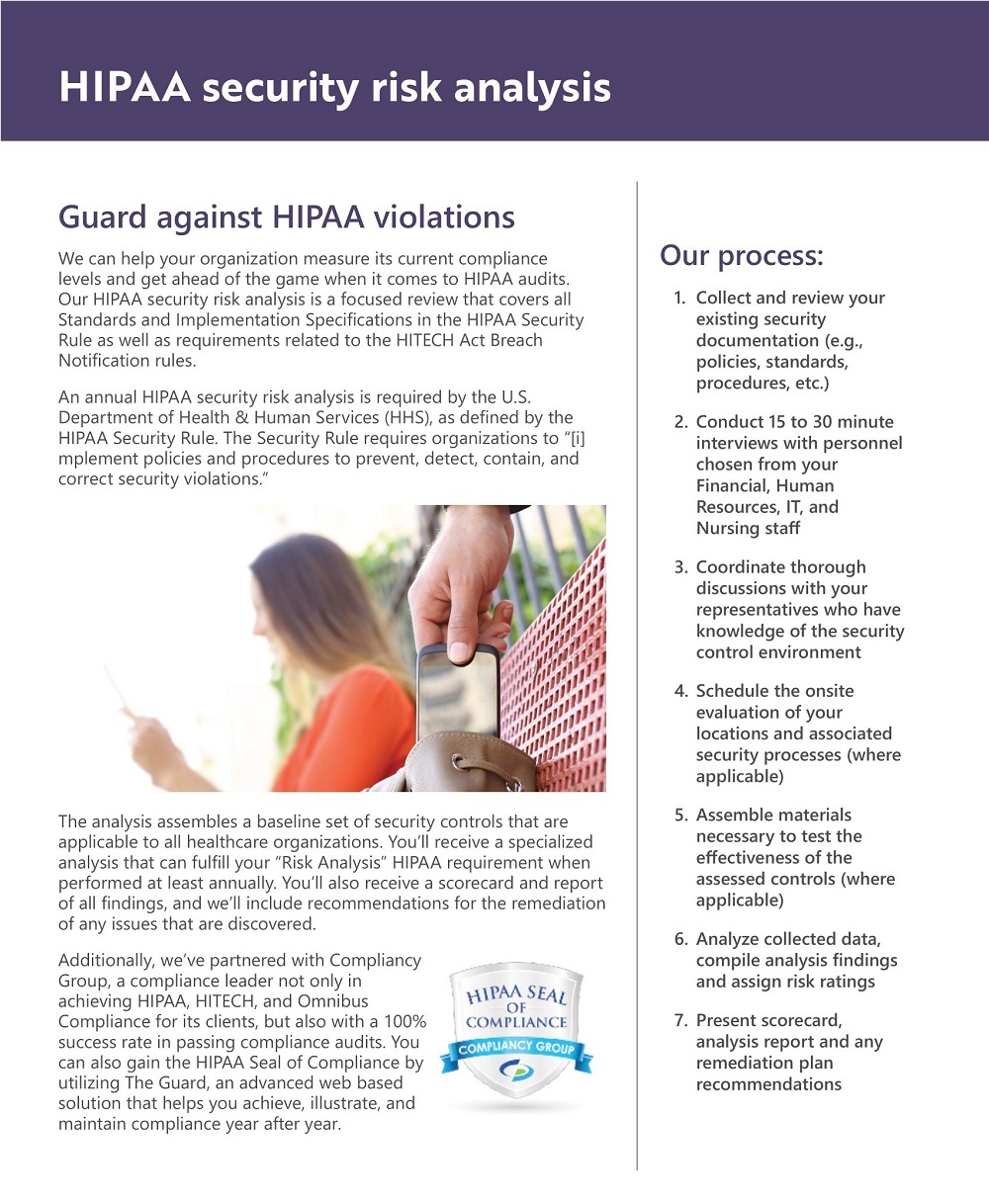
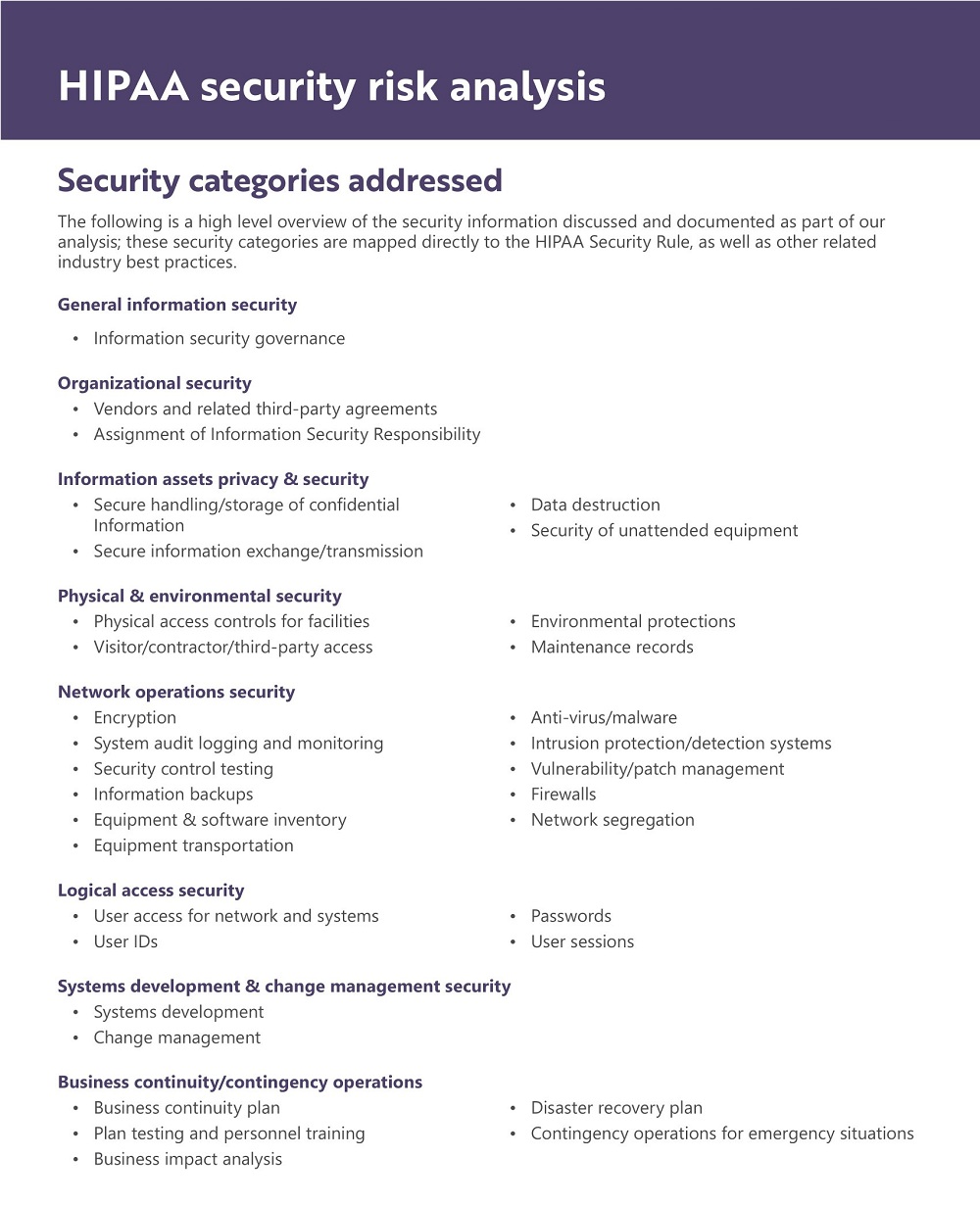
HIPAA Security Risk Analysis Template
|
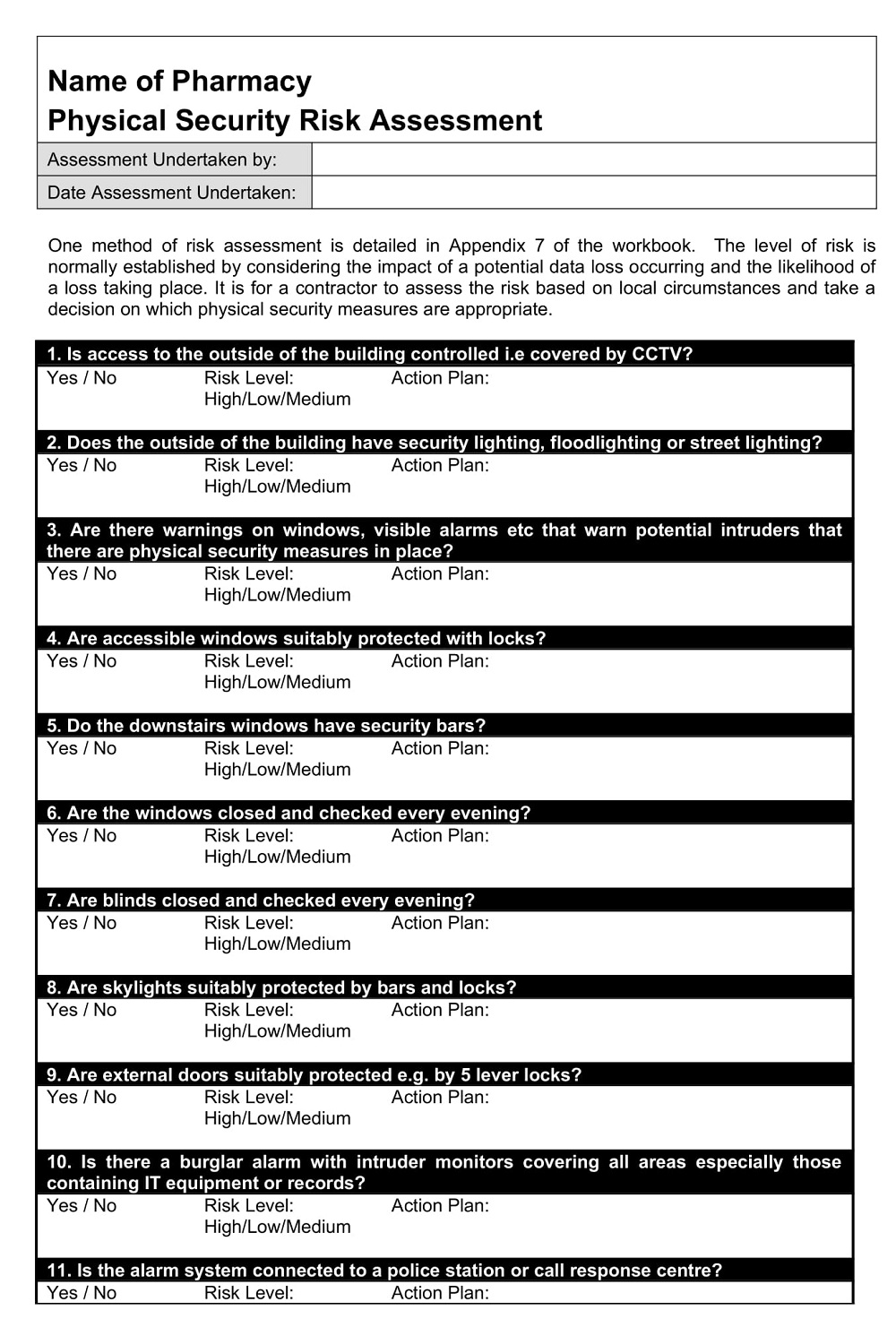
Physical Security Risk Assessment Template
|
Sample Security Risk Analysis Template
|
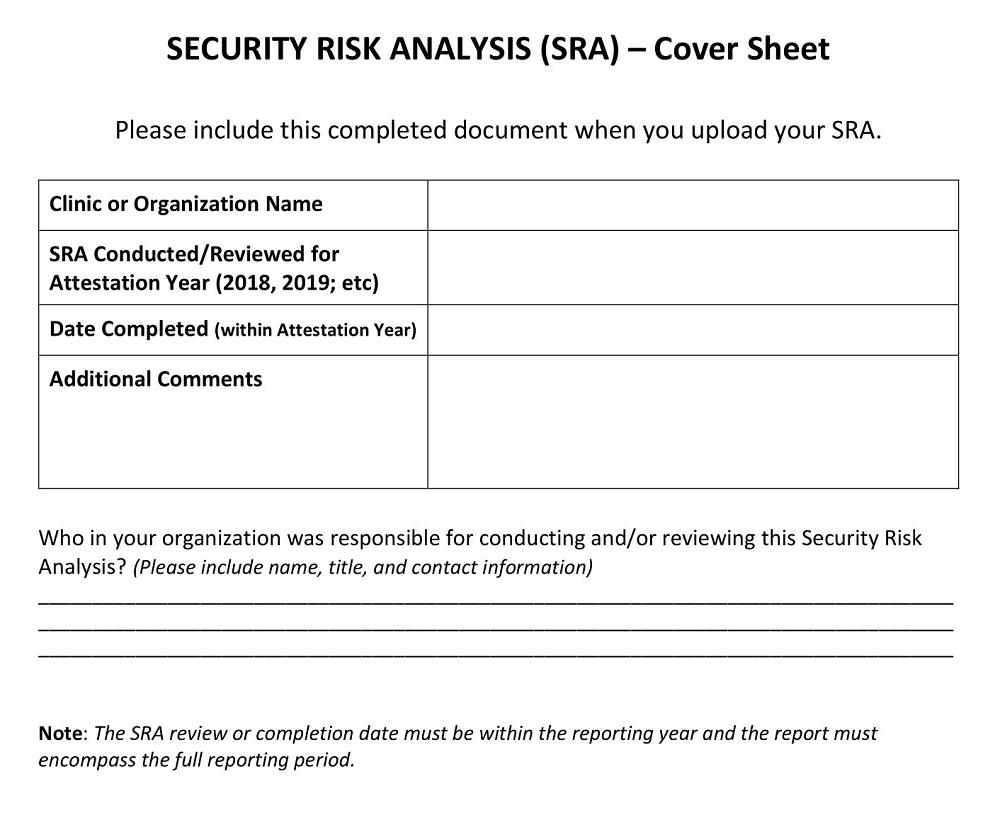
Security Risk Analysis Cover Sheet
|
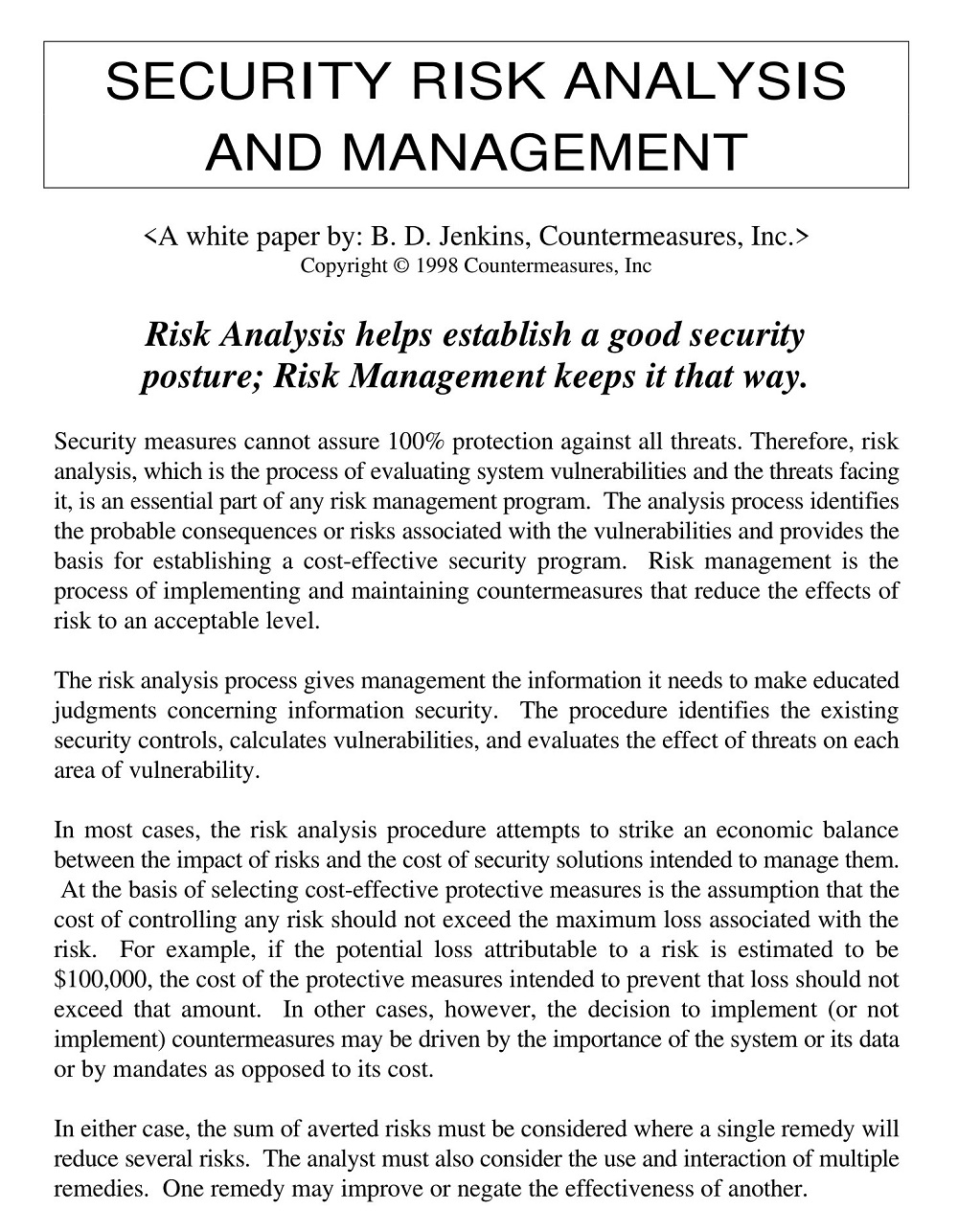
Security Risk Analysis Management
|
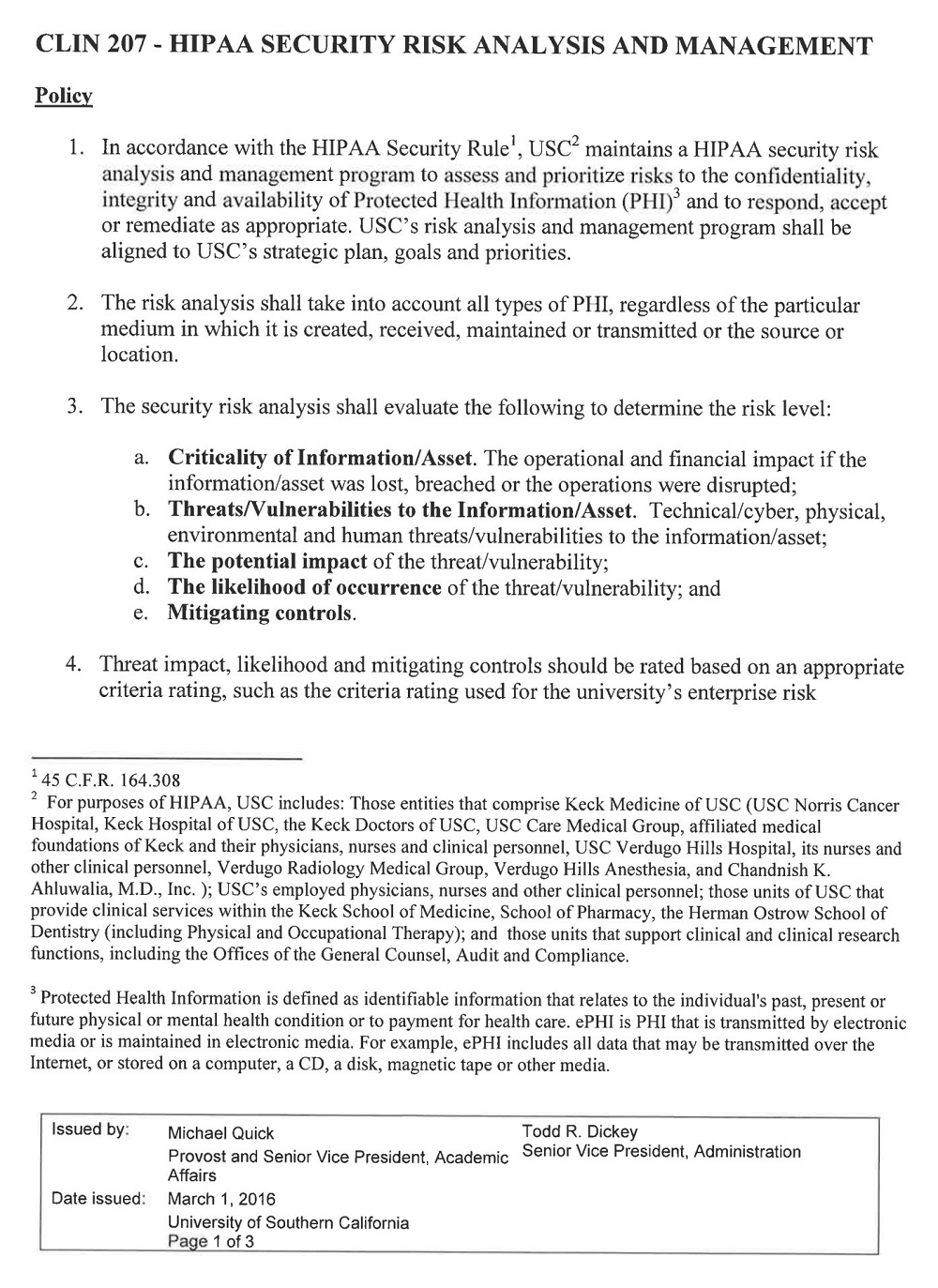
Security Risk Analysis Policy
|
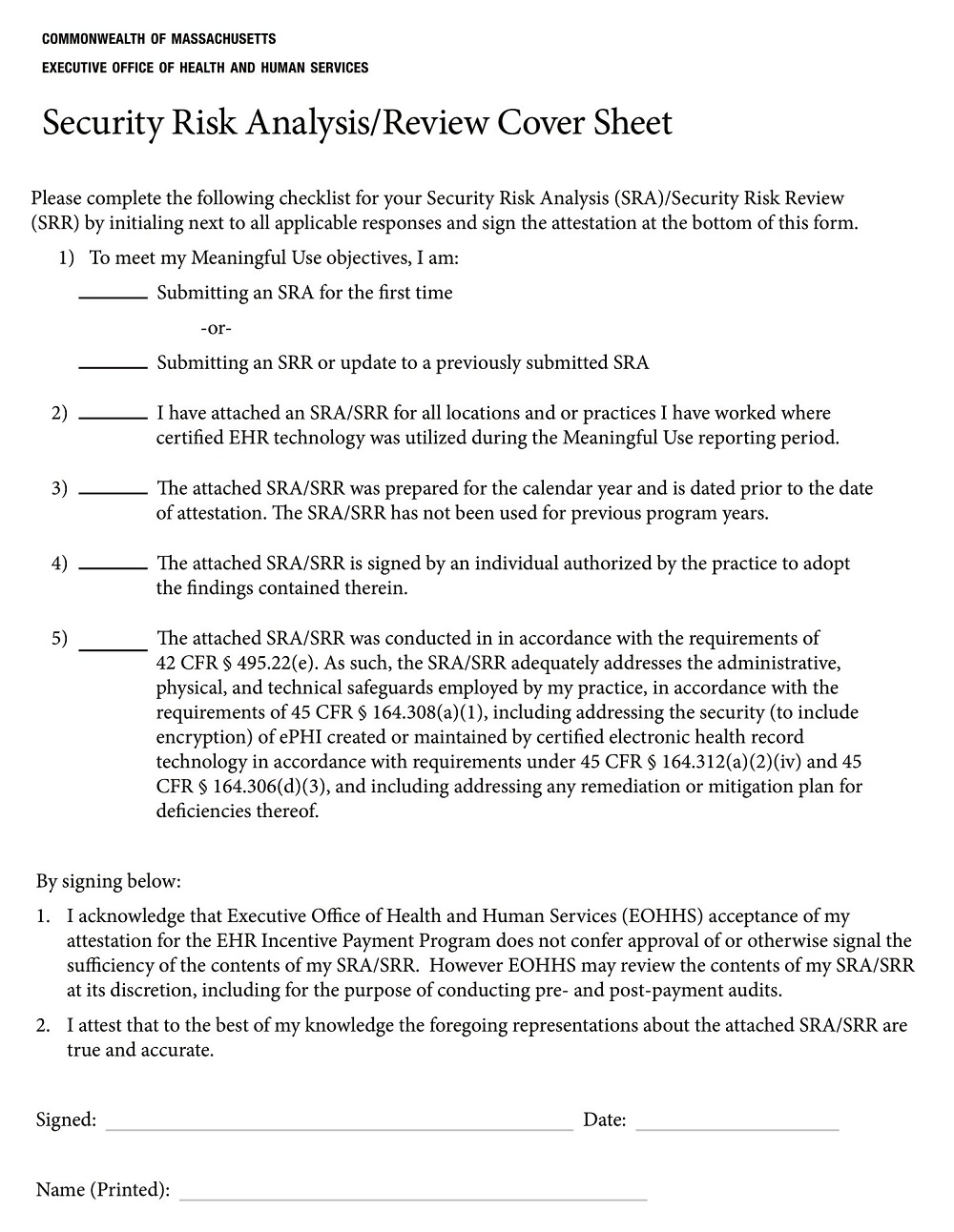
Security Risk Analysis Review Cover Sheet
|
Security Risk Analysis Template PDF
|
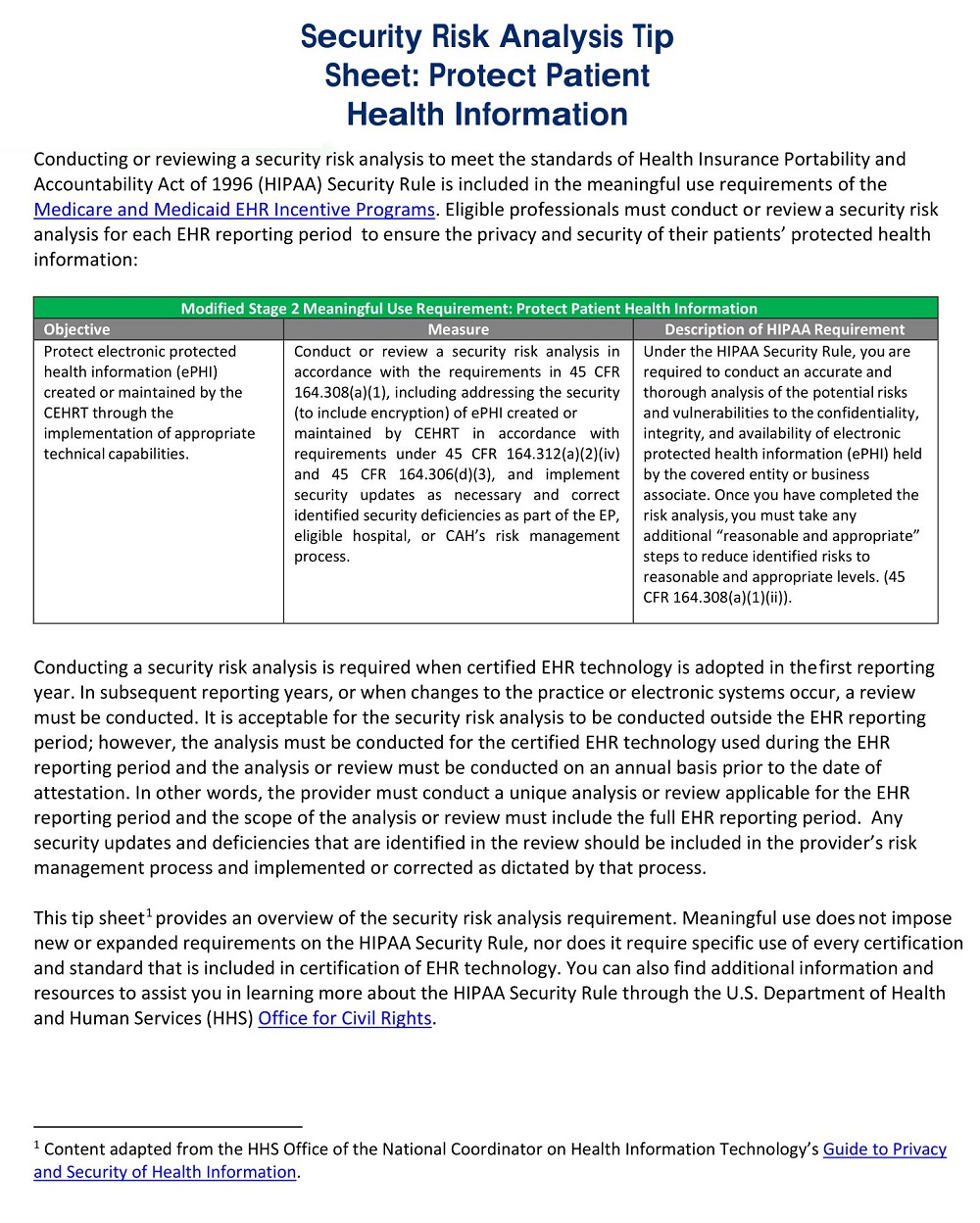
Security Risk Analysis Tip Sheet
|
Security Risk Assessment and Risk Management Plan
|
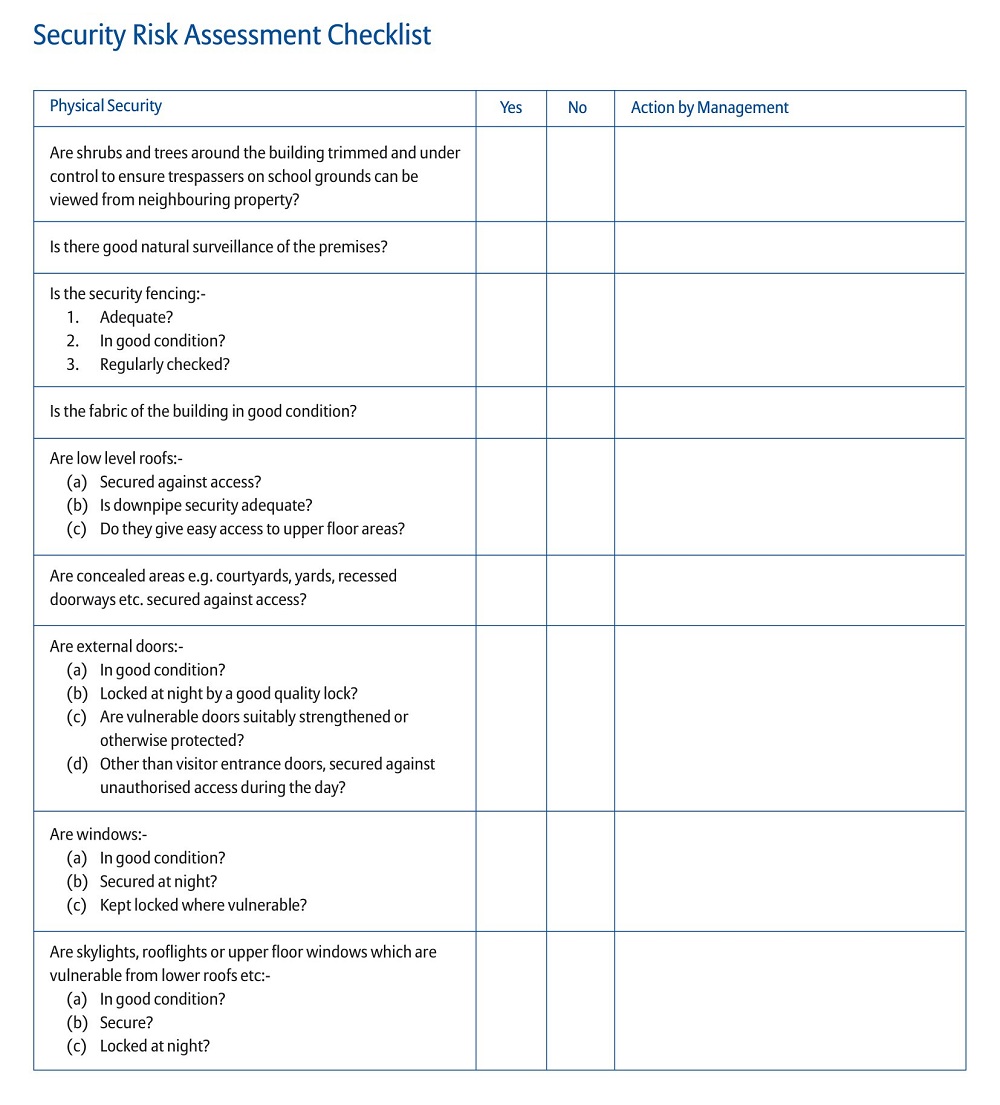
Security Risk Assessment Checklist
|
Security Risk Assessment Report
|
Standard Security Risk Analysis Template
|
System Security Risk Analysis Template
|
What is a Security Risk Analysis?
Security risk analysis is essential to protecting any organization as it identifies potential security threats and vulnerabilities that should be addressed. Through various methods such as vulnerability scanning, asset valuation, threat assessment, security control testing, and business impact analysis, an organization can become aware of possible risks they may face that they were not previously aware of. This process helps prepare the organization by providing insight into how their current security measures measure up and what further steps need to be taken to protect the organization against malicious actors. The security risk analysis process is invaluable for organizations looking to protect their data from unauthorized access or other malicious activities.
Scope Of The Security Risk Analysis
Security risk analysis helps to identify potential threats and assess the risk of those threats. It is an essential part of a security program and helps organizations prepare contingency plans for different scenarios. The scope of the security risk analysis will vary depending on a variety of factors such as the size and complexity of the organization, type, and location of data, nature of operations, etc. An effective security risk analysis may also include system reviews, employee background checks, internal audits, interviews with staff and managers, physical inspections of premises or systems, and business process reviews to determine possible vulnerabilities. With the proper implementation of security risk management policies and procedures based on best practices, organizations can protect their sensitive information from potential attacks.
Importance Of Conducting A Security Risk Analysis
Security risk analysis is critical for businesses and organizations in today’s world of ever-evolving cyber threats. Understanding the various risks associated with online data is paramount, as a breach of security can result in significant damage to a company’s reputation and financial standing. Such an analysis helps determine vulnerabilities relating to networks, systems, applications, and data that can help identify and prevent potential threats, identify protective measures needed to reduce or eliminate identified risks, monitor access rights of personnel to sensitive data for compliance purposes, and document all procedures for troubleshooting when issues arise. Without taking this precautionary step companies are often left ill-prepared to face new breaches or other looming cyberattacks which can be extremely costly.
Creating a Security Risk Analysis Template
If you’re trying to protect your business from cyber threats, then having a security risk analysis template is essential. A security risk analysis template helps you assess the risks of potential security incidents and provides you with a framework for responding to any threats that arise. In this blog post, we’ll explain how to create a security risk analysis template and why it’s important for your business.
Identify Your Assets and Weaknesses
The first step in creating a security risk analysis template is to identify the assets that need protection and the weaknesses that could be exploited by malicious actors. This includes all sensitive data, such as customer information, financial records, and trade secrets; physical assets like computers and servers; and any proprietary software or applications used by your company. You should also consider non-digital assets, such as employee access badges or paper documents. Once you’ve identified your assets and weaknesses, you can move on to the next step.
Assess Your Risks
Once you know what assets you need to protect, it’s time to assess the risks associated with each asset. To do this, think about the types of attacks that could be used against each asset and list out possible scenarios. For example, if an attacker were targeting your customer database, they may use phishing emails or malware-infected USB sticks to gain access to sensitive information. Other common attack types include SQL injection attacks, cross-site scripting (XSS), denial of service (DoS) attacks, or brute force attacks. By listing out these attack scenarios in advance, you can quickly respond if any of them occur in the future.
Create Your Plan of Action
Once you have identified all potential risks associated with each asset, it’s time to create an action plan for addressing those risks. This plan should include steps for identifying any vulnerabilities in your systems and procedures; implementing measures to protect yourself from those vulnerabilities; monitoring your systems regularly for signs of intrusion; responding quickly when suspicious activity is detected; notifying law enforcement if necessary; and updating your systems regularly with new patches and software updates. All of these steps should be documented in an easy-to-follow security risk analysis template so that anyone on your team can follow it in case of an emergency.
Methods For Analyzing Security Risks
Identifying and analyzing security risks can be a daunting task, but with the right methods, it can be much easier. Security professionals utilize both qualitative and quantitative techniques to evaluate the vulnerabilities associated with a system or application, such as exploring its design principles and conducting penetration and vulnerability tests. Additionally, organizations often employ threat modeling to assess which attack vector is most likely to be used by an attacker. An effective tool for this process is STRIDE, which helps identify potential threats based on categories of spoofing, tampering, repudiation, information disclosure, the elevation of privilege, and denial of service. By leveraging these methods and their accompanying tools, analysts are better informed to make decisions that will protect their organization from security risks.
Reference Link